Submitted by DataRecoveryGroup on
When scandals such as the Penn State University case or tragic events such as the mass shooting in Aurora, Colorado happen, news outlets and individuals scramble to see who can discover what. In many cases, emails, photos, and other data can be found by the right people with a few clicks and keystrokes. Such files often provide evidence needed for trial and the truth the public craves.
Jerry Sandusky
After word was out that Jerry Sandusky, a retired assistant football coach at Penn State, allegedly abused young boys for over a decade, people wanted answers. The resounding question was if officials including Joe Paterno, the once-respected Penn State football coach, knew about the abuse and covered it up.
At the beginning of July, emails dating back to 2001 were provided to CNN and allegedly contained dialogue that confirmed Penn State university officials knew about Jerry Sandusky’s crimes and decided to conceal them rather than alert authorities. The contacts include former Penn State President Graham Spanier, former Senior Vice President Gary Schultz and Athletic Director Timothy Curley.
Although the origins of those emails are unclear, another private investigator hired by Penn State, Louis Freeh, said he and his team found similar, if not the same, incriminating emails and files during their investigation. The emails, which Freeh called “the most important evidence in the report,” during a press conference on July 12, demonstrated Paterno followed the Sandusky investigation and persuaded officials not to formally report him to law enforcement back in 2001.
In a confidential file uncovered during the Freeh investigation, Schultz made notes on Sandusky’s poor judgment and questioned if it was the opening of Pandora’s box and “other children?”. In the same July 12 press conference, Freeh said Schultz had made an effort to conceal those files. The Freeh investigation involved reviewing more than 3.5 million documents total.
James Holmes
Tragic or not, when someone does something newsworthy and makes national headlines, the first place to look for information on that person is the internet. Doing some background research is as easy as bringing up Google, typing in the name and perhaps a few keywords, and hitting enter.
Within hours of the movie theater shooting in Aurora, news outlets reported that James Holmes, the alleged mass killer, had a bachelor’s degree in neuroscience and recently dropped out of a Ph.D. neuroscience program at the University of Colorado.
Although Holmes did not have accounts on social media websites, or much of a web presence at all, those are often the first places people flock to when trying to discover information about a person. In this case, many believe he might have used a different identity online.
However, one online profile of Holmes was found – on AdultFriendFinder.com, a website that calls itself “the world’s largest sex dating site and swinger personals community.” According to three unidentified women, Holmes contacted them but was shot down. His profile has since been taken down, but not before it was confirmed it was his and screen shots were posted all over the internet.
Although the University of Colorado has been barred from releasing any records about Holmes, including his university email account, journalists and interested parties will no doubt keep digging. His computer was seized by authorities and time will tell what it contains.
During the computer examination, authorities will undoubtedly look for purchases he made on the internet. Recently, Aurora Police Chief Daniel Oates said Holmes ordered more than 6,000 rounds of ammunition on the internet in the past couple months.
So What Is Involved?
Activities such as normal web browsing and email can leave a lot of data on computers. Even when a file is deleted off of a hard drive, some information about it remains, just in a different form. Such files may seem gone or be in a non-readable format, but they can be recovered; this is something most nontechnical criminals do not often think of.
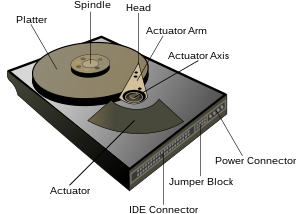
When it comes to examining computers for incriminating files, methods could be as simple as reading data normally (checking email and documents, etc.) or as complicated as actually recovering lost data (finding overwritten files, recovering data from a broken or damaged hard drive).
Most data recovery efforts involve looking in the right place on the computer hard drive to find where information traces have been stored. In the case of Sandusky, original email files might have been saved in his inbox or recovered from his Internet Service Provider's, or ISP’s, mail server.
Although Holmes’ computer was intact when they found it, his apartment has been booby-trapped. If his computer had been blown to pieces, there is a chance they could have recovered data from the hard drive through a more in-depth process.
A seemingly-destroyed hard drive can sometimes be carefully taken apart and read. This may involve taking pieces out and putting them in a new hard drive or installing a new circuitboard. Most people are unaware that hard drives are extremely durable and files often can be recovered in the case of fire damage, water damage, and many other sorts of natural disasters.
Although most of us will probably never be directly involved in such high profile cases, it’s still useful to be cautious when working on a computer and cognizant of the fact that it’s very difficult to delete all traces of activity.